Ever wondered what’s inside blockchain?
Well, we know that blockchain technology is all about linear chain of blocks that contain data, which is extremely difficult to change, i.e. immutable. The thing that is unclear is how the data is made immutable.
The mystery lies in the architecture of blockchain.
The following article discusses all you need to know about how blockchain works and makes data immutable.

Organizations spend billions on cyber-security solutions in order to keep their sensitive business data tamper-free. But often it happens that their data gets manipulated, replaced, or falsified. In most of the cases, this is due to the lack of security in data transfer and storage.
With blockchain development, organizations can bring immutability into play!
This is because blockchain is structured in a way that once data is recorded on it, that data can’t be technically altered. Organizations can leverage this and ensure that no one can intrude in their system or modify their valuable data.
So what does blockchain architecture look like?
Before we dive into the architecture of blockchain, it is important to logically understand what type of data is stored by blockchain.
What data is stored by blockchain?
Blockchain is a write-once, read-only database that stores data in uniform-sized blocks – it is an ever-growing database where new blocks are added constantly over time.
Usually, each block contains the following key pieces of data:
• Version
• Timestamp
• Hash
• Difficulty-Level
• Nonce
• Merkle Root
• Transaction Data
• Version: It refers to the version number of the block.
• Timestamp: The timestamp marks the time of each transaction. In a way, it proves when and what has happened on the block.
• Block Differentiator or Hash: Each block stores a unique code known as “hash,” which uniquely identifies data or transaction. It can be called as the backbone of a blockchain network. (Detailed explanation is provided in the next section)
• Difficulty-Level: It refers to the level of difficulty of how hard it is for miners to solve the block.
• Nonce (or “Number Only Used Once”): It is a one-time code that is used to modify the output of a function – it ensures that the same encrypted value (like username and password) can’t be submitted to the server again. Even with the same data, the server will expect a different value due to the modification made by the nonce. (Detailed explanation is provided in the next section)
• Merkle Root: As mentioned above, every transaction has a hash associated with it. In a block, all of the transaction-hashes are themselves hashed and the result is the Merkle root. In simple words, the Merkle root is the hash of all the hashes of all the transactions in the block. (Detailed explanation is provided in the next section)
• Transaction Data: Each block holds a list of transactions. The order of transactions present in every block is based on the course of the addition of a transaction to the block.
Now that you have a basic idea about what sort of data is stored in each block, let’s move to the architecture, i.e. the container that holds all of the above pieces of data.
Looking for scalable Blockchain development services?
Send us your inquiry.
Architecture of Blockchain Explained
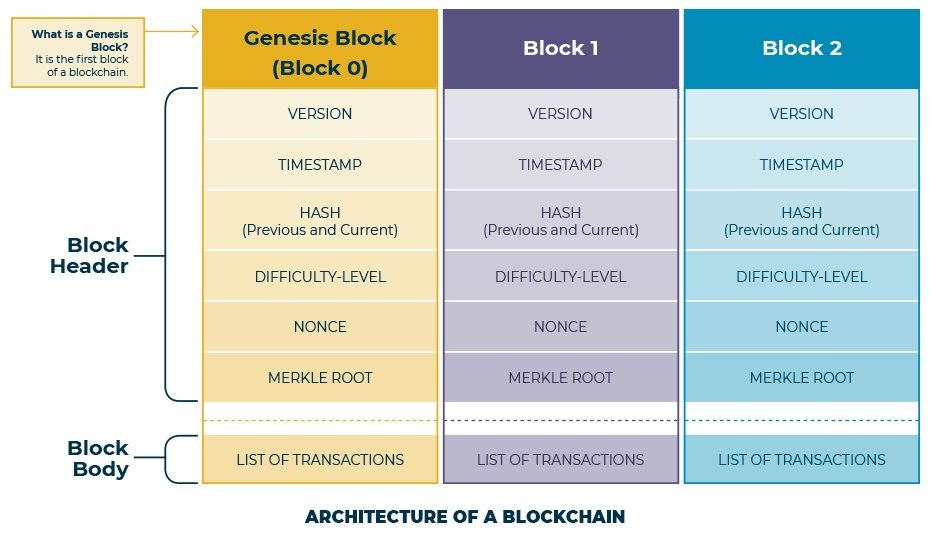
In a blockchain network, transactions are validated by a group of nodes and then recorded in a block. Each block inside the blockchain is composed of a header and a body.
What is a Block Header?
The block header is made up of metadata (data about data). It helps to verify the validity of a block.
As you can see in the architecture diagram, the block header of a block consists of:
• Version
• Timestamp
• Hash
• Difficulty-Level
• Nonce
• Merkle Root
What is a Hash? Why it is called as “the backbone” of a blockchain network?
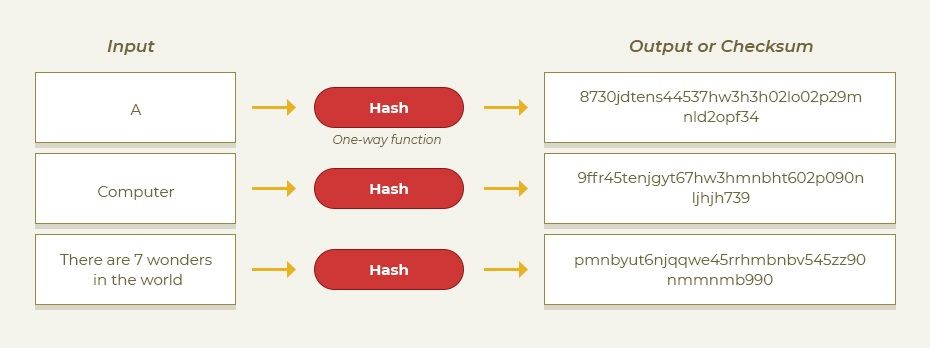
A hash is a cryptographic algorithm or function that converts an input string (numbers, alphabets, media files etc.) of any length into an encrypted output or “checksum” of a fixed length. The process of applying a hash algorithm to any data is called hashing.
The checksum points at the exact data input — if just a single byte differs between two files, the outputs after hashing will be two completely strings. This means that a small change in your input can drastically change your output.
Different blockchains use different hashing algorithms. For example, if we talk about Bitcoin, it uses the Secure Hashing Algorithm 256 (aka SHA256), which produces a 32-byte hash.
The usefulness of the hashing process is that you can’t reverse-engineer a hash, i.e. you won’t be able to work backward from an output string to determine the input data.
Hashing is indeed an integral part of the blockchain. It is essentially a feature that gives security capabilities to the processed transactions, making them immutable. That is why it is called as the backbone of a blockchain network.
Previous Hash
Hashing of a particular block involves using the meta-data of the previous block while producing a new hash for it. This creates a link between the block and the chain and thus it becomes technically “unbreakable.” Hereafter, no one can delete or modify the data of the block stored in the blockchain; if someone attempts this, the successive block rejects the modification (as the hash of block won’t be valid any longer) – thus, if data is tampered with, the blockchain will break; this characteristic is not found in traditional databases, where information can be modified or deleted with ease.
What is a Nonce?
As discussed above, nonce is an abbreviation for “number only used once.” Technically, it is a pseudo-random number that is utilized as a counter during the process of mining.
As the hash value is the same no matter how many times it is calculated, the nonce is utilized to change the value and search for a number which is lower than the difficulty.
Too much technical? Well, here’s a simplified explanation:
In proof-of-work systems like blockchain, a nonce is used to make the task of generating a valid hash more difficult. This means that blockchain miners need to find a nonce value that, when merged with the hashing algorithm, generates an output that meets certain requirements.
What is a Merkle Root?
In order to understand what a Merkle Root is, you need to first understand the concept of Merkle Tree.
Merkle Tree
A Merkle Tree, or binary hash tree, is used to encrypt the blockchain data in a secure and efficient way. It facilitates quick verification and fast movement of large sets of blockchain data (from one node to the other on the blockchain network).
A Merkle Tree is constructed through bottom-up approach by repeatedly calculating hashing pairs of nodes until there is only one hash left.
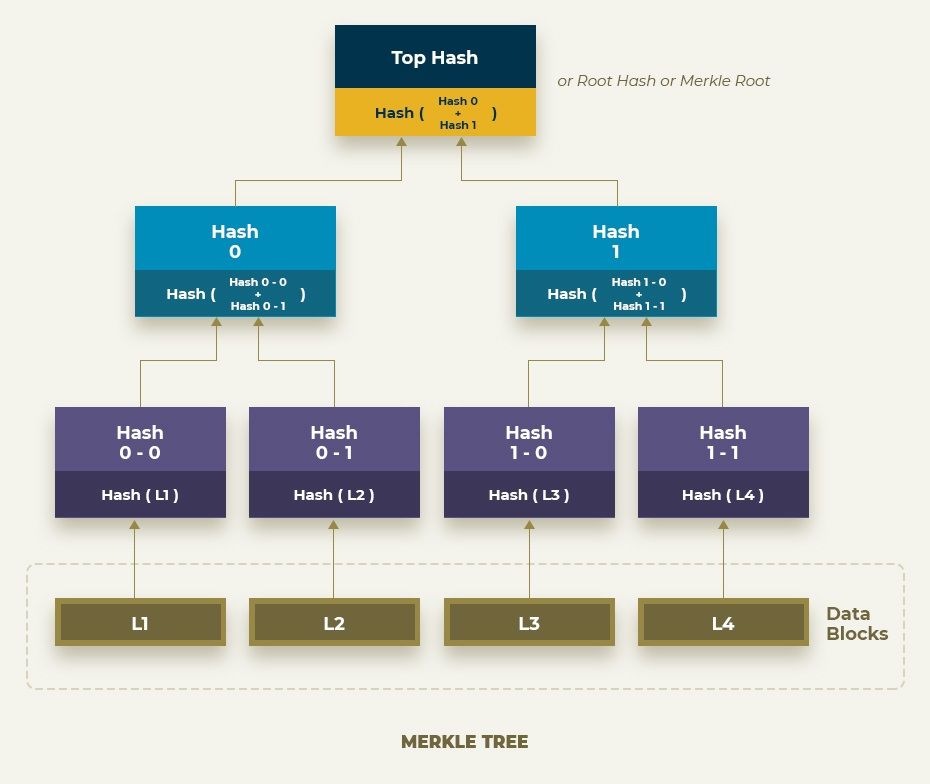
In the above tree diagram, we can observe that input of data is broken up into blocks labelled B1 though B4. The first step is to hash each data block using a particular hashing algorithm (e.g. MD5, SHA256, SHA1, and SHA512). With this, the blocks Hash 0-0, Hash 0-1, Hash 1-0, and Hash 1-1 are created. This is the primary step for developing a Merkle Tree. These blocks can be referred as leaves of the Merkle Tree. There must be at least two leaves (there isn’t any upper limit).
Next, two adjacent hashes are merged into a single hash. So, Hash 0-0 is chained with Hash 0-1 and is hashed again by means of a hashing algorithm. The result is Hash 0. Similarly, Hash 1-0 and Hash 1-1 blocks yield Hash 1. The process continues until a single hash is generated. The final hash what you get is referred to as Merkle Root.
Hence, we can say that a Merkle Tree formation is the process of making a single hash from a group of hashes.
Merkle Root
The single hash that is produced by the Merkle Tree is called the Merkle Root. Each block in a blockchain has exactly one of it – it is like a fingerprint for all the transactions in a block.
A Merkle Root is used as one of the fields in a block header in order to have a short representation of every transaction inside the block.
What is a Block Body?
The block body is composed of a transaction counter and transactions. The maximum number of transactions that a block can hold depends on the block size and the size of each transaction.
Conclusion
It is the blockchain architecture that makes it the most difficult thing to change – it is developed such that in order to tamper the data without following protocol rules would require someone to have access to an energy source and to computer power that exceeds that of the entire network, which is almost impossible. That is why we can say that blockchain is structured to guarantee immutability.
Talk with one of our solution architects.Planning to leverage the capabilities of Blockchain?



